Happy Thanksgiving! 🦃 As we approach the holidays, we will see an uptick in scams and fraud… here is a quick guide:
Although many of us have good security on our corporate systems such as 2FA, SSO, and VPNs/Zero-Trust networking… we sometimes neglect our personal security. As you or your company gains prominence in the market (congratulations)... executives and their employees will begin to see a rise in “smishing” attacks.
Unfortunately this is a common occurrence these days, and there isn’t much to do after the fact to prevent (never click or respond of course). However, this is a guide to help prevent the proliferation and impact of these types of attacks.
Smishing Attack Overview
Smishing, similar to email phishing, is where an attacker attempts to spoof a message from someone via Texting / SMS in order to get the recipient to take an action.
Example actions include:
Purchasing a small item like a gift card
Harvesting online credentials to banking and financial institutions
Gathering personal information for secondary attacks like spoofing the IRS, or a FedEx/Amazon shipment
The best protection against these attacks is to:
Quickly recognize the attack and NOT respond or click links
Report the sender to your provider as spam and malicious
Similar attacks are simple mass emails (with no body) to contacts of executives via email. These are likely an effort to confirm emails.
Let’s step back for a second though and go over ways to prevent attackers from accessing this data in the first place as well as protect our personal accounts from attackers.
Personal Security: 2FA On Critical Accounts
Talk to any security professional and they will tell you to start with 2FA (Two Factor Authentication) on all your accounts. As with anything, you need to start somewhere, so the best place to start is in the following places:
Personal email like Gmail, Outlook.com, or other areas
Banking and Financial sites
Social media sites like LinkedIN, Facebook, etc
It’s important that you do not use SMS for texting. Make sure to usa a TOTP (Time Based One Time Password) based method for 2FA, or in other words using something like Google Authenticator or Authy where you scan a QR code (the secret) and it generates a new number every minute.
SMS is no longer considered a best practice due to SIM Swap Attacks.
Her is a nice intro video I like to use in my security awareness talks and classes on how easy an account take over is:
If you have the time, here is a video of an actual SIM Swap Attack and the impacts of such an attack:
These videos are meant to educate you and provide awareness, and not scare you.
Personal Infosec: Password Hygiene
Password recommendations and hygiene has changed over the past few years, but unfortunately I’m still hearing bad advice out there, so here is a distilled version of the latest guidelines...
Length > Complexity
Complex characters are statistically not as important as password length
Min recommended length is 12 characters (spaces included!)
Example: “My Little Brother Bit My Finger And It Hurt!!@#$” is generally better than “LittleBro1.”
Do not use the same password on multiple sites
Use a password manager to manage most of your passwords
Only passwords you might want to remember are your Gmail and password manager for example
No need to rotate passwords if you have 2FA enabled
As a good practice though, change your password after enabling 2FA in case it was old and overused
Do not share passwords
Have everyone with their own passwords
If you must share, use a shared vault and add 2FA. 1Password for example will store and generate the 2FA code for example
If you refuse to use a password manager, then use an algorithm for remembering passwords. For example:
Pick a base for your password - like “Th4nk5G1v1ng!” or the one above
Add an extension for any various website - Like “GM21.” for Gmail or “IC21.” for iCloud
Yes you will encounter websites and people that are not caught up on the latest recommendations. That’s ok, just guide them with care and ease. Even this guide will get outdated, so I might need a nudge to update it. 😇
Personal Infosec: LinkedIN Security
I’d like to talk specifically about LinkedIN security as this is an area often overlooked by most executives, staff, and employees. Even with 2FA enabled, there are privacy options overlooked that will leak your personal information such as phone numbers and your personal email address.
Here is a quick walkthrough… everything can be found in the Settings & Privacy section, under Account:
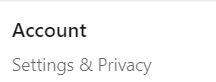
Account Access
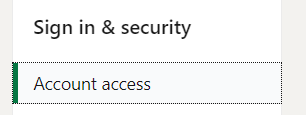
Primary Email Address
Many people overlook this section, but you will notice a collection of email addresses tied to your LinkedIN profile over the years. I had 8 at one point!

LinkedIN Security: Visibility
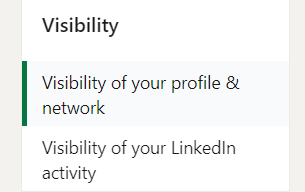
Email address
With automations now being ubiquitous, data is harvested at astonishing speeds. No longer is it someone sitting there pulling your information, it’s all pulled via API’s and 3rd parties in bulk. This section is important.

Personal Information Security Summary
As you can see your digital footprint and trails can be pretty big. Each footprint you leave has several other trails and sometimes grows legs without you knowing. Companies will constantly add “features” (you’re not the only customer 😉) making your data even more accessible to 3rd parties.
Attackers use these same tools. It’s very cost-effective for them to just pay for LinkedIN Premium or Sales Navigator or whatever other tool out there and just get all high quality and legitimate data.
If you see anything I may have missed, please let me know in the comments below or directly.